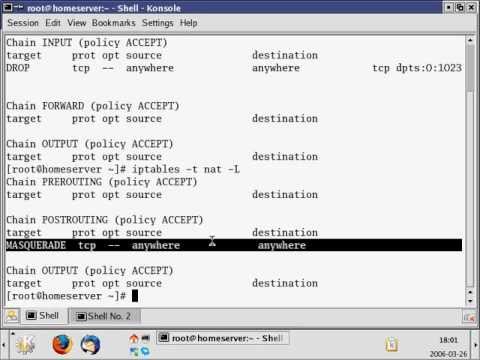
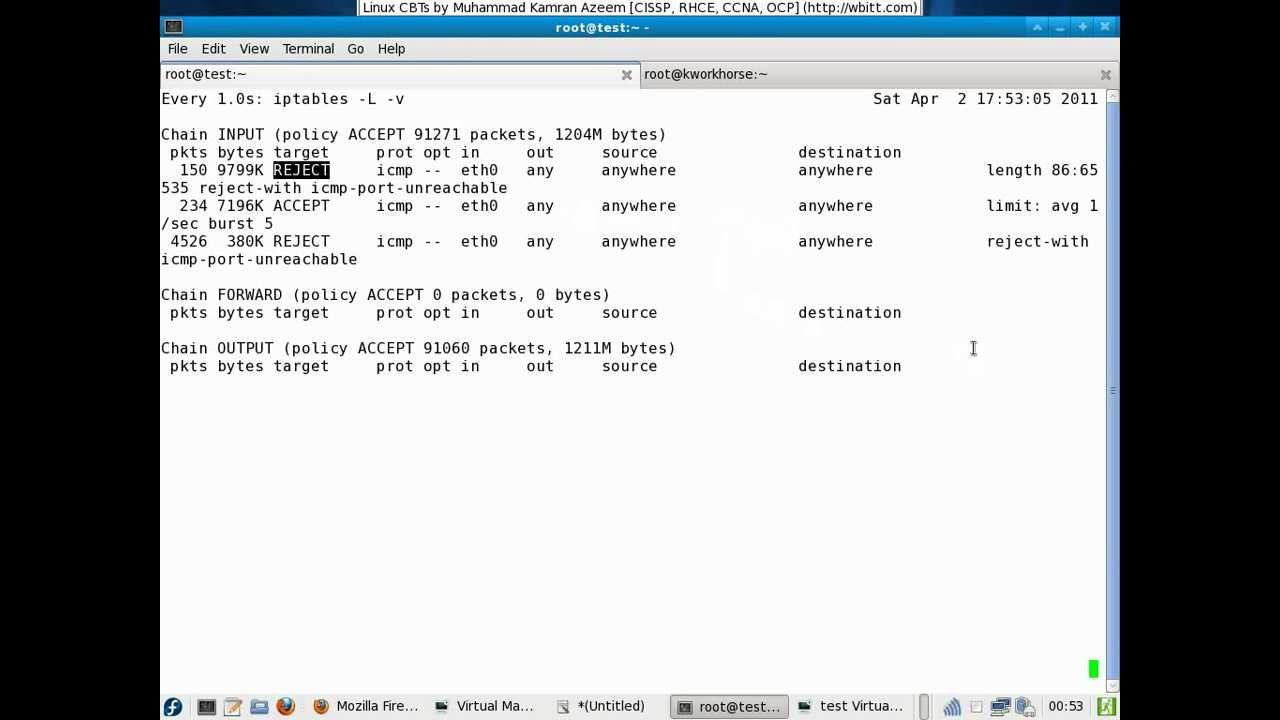
Urdu CBT Linux System Administration SQUID 2/15 Transparent Proxy
This is an old CBT (created in 2006). It explains how you can configure squid cache service. This video covers transparent proxy. Author: Muhammad Kamran Azeem Courtesy: http://wbitt.com